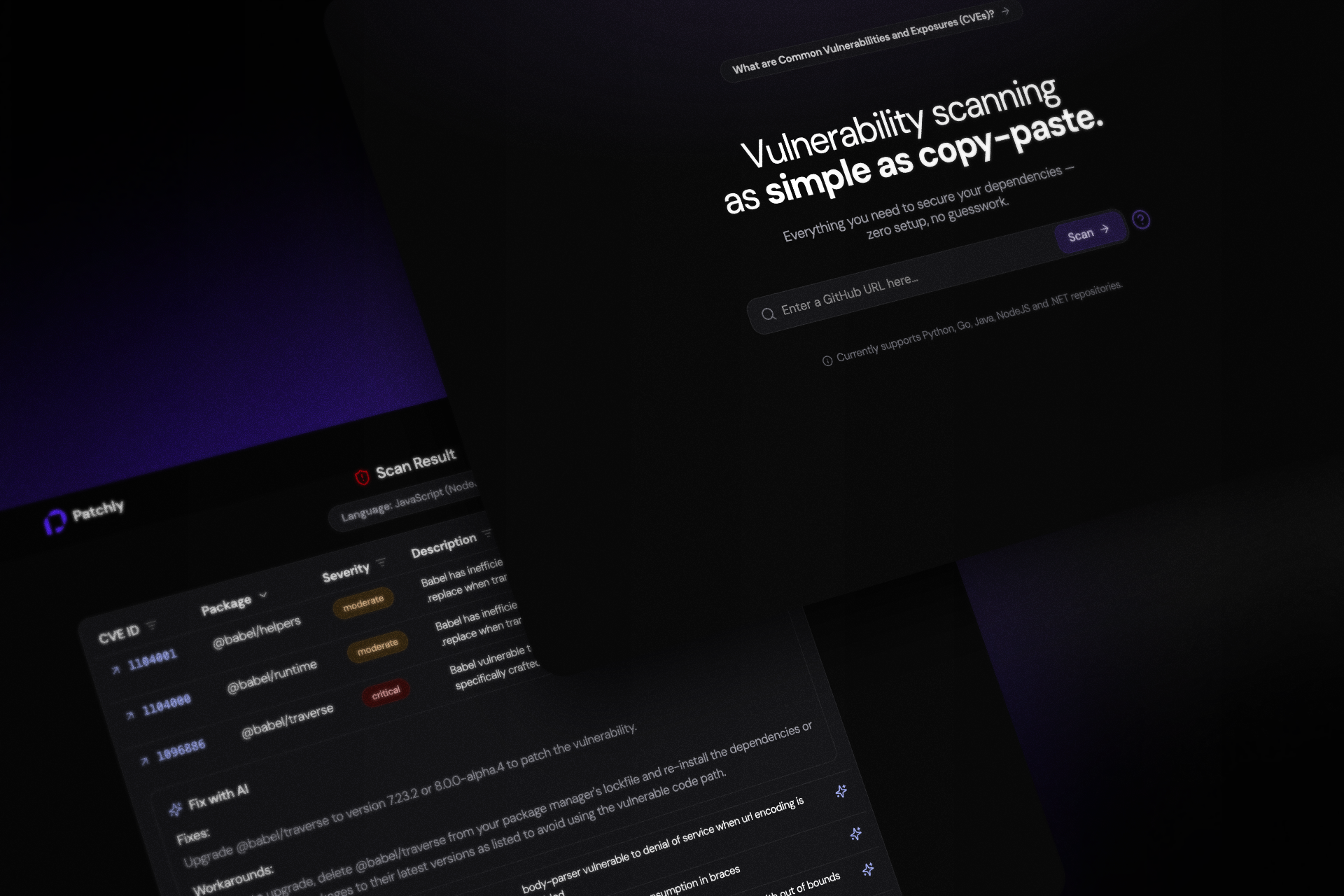
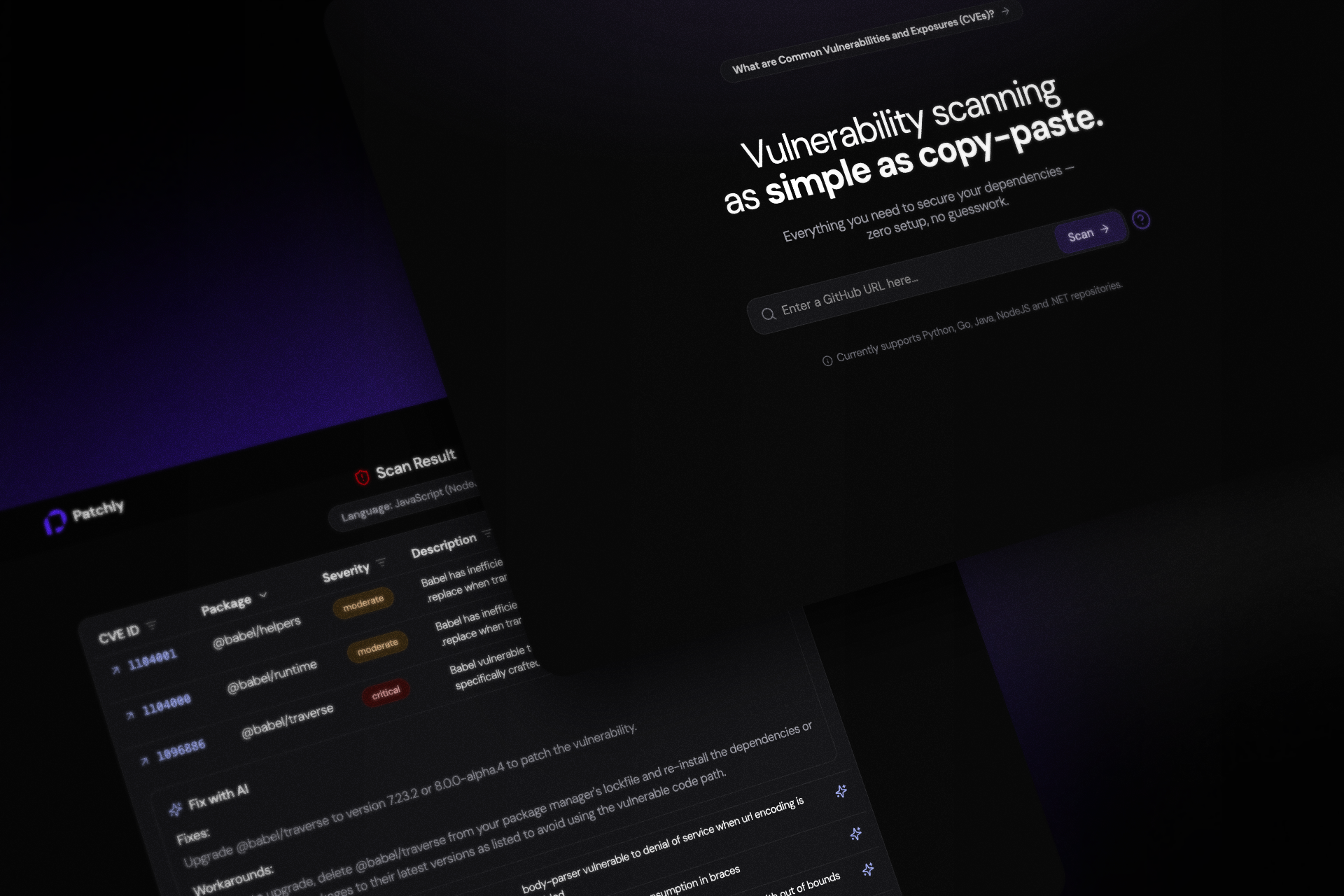
Patchly
2025
Timeline
June 2025
Overview
Patchly is an AI-powered vulnerability scanner that analyzes GitHub repositories in real time, eliminating manual cloning while detecting insecure dependencies and providing context-aware fixes through an interactive dashboard.
Technologies
PythonFastAPIOpenAI APINext.jsTailwind CSSVercelRender